Post-Quantum Safe Cryptocurrency
Tidecoin is a decentralized currency blockchain with a post-quantum secure signature.
Tidecoin’s currency design enables it to run on various ubiquitous computing devices, enabling a pervasive process of value, even that in multiple worlds.
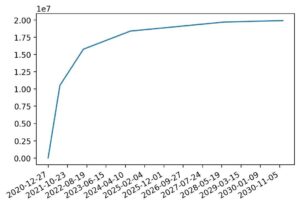
Total supply: 21 million coins
Circulating supply: 16 million
|
|
Exponential halving time / CPU Mining / Community driven / Anonymous creator / Future-proof
falcon
Fast-Fourier Lattice-based Compact Signatures over NTRU

Falcon is a cryptographic signature algorithm submitted to NIST Post-Quantum Cryptography Project on November 30th, 2017. It has been designed by: Pierre-Alain Fouque, Jeffrey Hoffstein, Paul Kirchner, Vadim Lyubashevsky, Thomas Pornin, Thomas Prest, Thomas Ricosset, Gregor Seiler, William Whyte, Zhenfei Zhang.
The point of a post-quantum cryptographic algorithm is to keep on ensuring its security characteristics even faced with quantum computers. Quantum computers are deemed feasible, according to our current understanding of the laws of physics, but some significant technological issues remain to be solved in order to build a fully operational unit. Such a quantum computer would very efficiently break the usual asymmetric encryption and digital signature algorithms based on number theory (RSA, DSA, Diffie-Hellman, ElGamal, and their elliptic curve variants).
Falcon is based on the theoretical framework of Gentry, Peikert and Vaikuntanathan for lattice-based signature schemes. That framework instantiated over NTRU lattices, with a trapdoor sampler called “fast Fourier sampling”. The underlying hard problem is the short integer solution problem (SIS) over NTRU lattices, for which no efficient solving algorithm is currently known in the general case, even with the help of quantum computers.
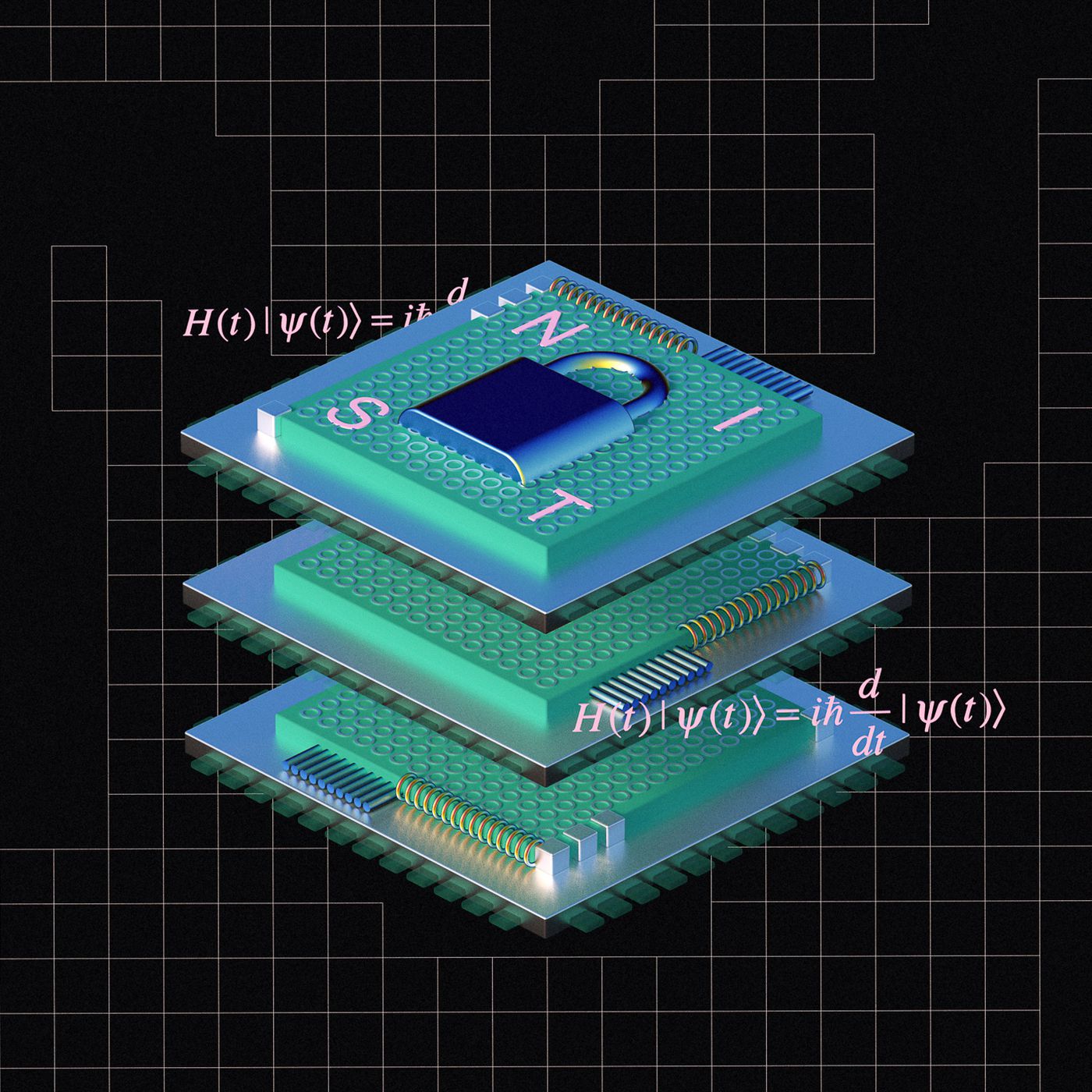
Falcon offers the following features:
- Security: a true Gaussian sampler is used internally, which guarantees negligible leakage of information on the secret key up to a practically infinite number of signatures (more than 264).
- Compactness: thanks to the use of NTRU lattices, signatures are substantially shorter than in any lattice-based signature scheme with the same security guarantees, while the public keys are around the same size.
- Speed: use of fast Fourier sampling allows for very fast implementations, in the thousands of signatures per second on a common computer; verification is five to ten times faster.
- Scalability: operations have cost O(n log n) for degree n, allowing the use of very long-term security parameters at moderate cost.
- RAM Economy: the enhanced key generation algorithm of Falcon uses less than 30 kilobytes of RAM, a hundredfold improvement over previous designs such as NTRUSign. Falcon is compatible with small, memory-constrained embedded devices.
Falcon is one of the winner from six-year competition of Federal agency reveals and is announced as one of four Quantum-Resistant Cryptographic Algorithmst, so FALCON passes all 4 rounds of selection for the new standard. Therefore FALCON is one of the Post-Quantum digital signature standards.
roadmap

Mobile wallet for Android

Coingecko and Coinmarketcap listing

Core wallet update
mining
Tidecoin is using CPU-friendly, GPU-unfriendly, and FPGA/ASIC-neutral PoW algorithm yespower.
In other words, it’s meant to be relatively efficient to compute on current CPUs and relatively inefficient on current GPUs.
The Tidecoin network was built on the premise that it is wasteful for the majority of users to contribute to special purpose mining equipment. The future, however, will see more specialized hardware used in larger numbers by pools.
It transitions gradually into a more distributed mining approach, using ASIC and/or FPGA hardware.
The use of specialized hardware will likely become more important as more users join Tidecoin in the future. Currently, tidecoins are mined primarily by ordinary computers and mobile devices.

NEWS
Quantum Computer Science
Quantum circuits researchers explore quantum circuits to make it easier for quantum computers to perform mathematical problems. In general, it can be said that almost
Quantum Computing and its potential applications
This article discusses quantum computing and its potential applications. A quantum computer is a computer that uses quantum mechanics, which allows it to perform calculations
Falcon Signature
This article discusses the Falcon cryptographic signature algorithm, which has been selected by NIST as a post-quantum cryptography standard. Falcon is based on the theoretical
Why Quantum Computing Could End Up Cracking Blockchain Wallets – Uncover the Unbelievable!
In recent years, the rise of blockchain technology has revolutionized the way we conduct transactions online. This revolutionary technology has made it possible to securely
Simply Tidecoin Mining
As mentioned in other articles, Tidecoin mining algorithm is ASIC’s neutral and gpu unfriendly. Therefore, private devices can be used excellently to mine the coin.Tidecoin
The human brain cannot imagine an Exponential Process
It presents us with dazzling challenges when we find the result that plants grow according to the e function. For us, the pond was “suddenly”
Closest Vector Problem
Tidecoin uses FALCON as the signature algorithm for the signature. FALCON uses a lattice-based approach.This article aims to briefly outline what mathematical problem is behind
Technical Characteristics of the Signature
Both new NIST crypto standards for signatures (FALCON and CRYSTALS-Dilithium) are particularly suitable for time-critical applications. [page 2] Both are based on the lattice-based cryptography
The Information Density in a Quantum Computer
An analog computer uses bits to represent information. A bit has a clearly defined status of 0 or 1. The step-by-step storage and forwarding of
Shor Algorithm- the nightmare for ECDSA
“The famous Shor algorithm allows an opponent to break ECDSA by a quantum computer that is sufficiently efficient.” page 269, Koustav Kumar Mondal and Deepsubhra
Lattice Based Encryption Example
This article should give a short example, how lattice based encryptions are working. Following parameters are given. n is the number of matrixes, which are
TIDECOIN is a new future
The World Economic Forum estimates that by 2025, at least 10% of the world’s GDP, currently at USD 100 trillion, will be managed via Blockchain